Adware Networks Hiding Behind Thousands of Domains
Published on March 26, 2025
We've been analyzing traffic in our RPZ DNS metrics via https://planisys.net/pdns, focusing on lookalike domains and a single recurring IP address.
This investigation revealed what appears to be a centralized adware and tracking infrastructure, comprising:
Over 32,700 domains so far
Spread across TLDs like .live, .online, .sbs, .shop, .site, .help, .icu, .space, .store, .support, .com, .net, and more
We found 654,000+ domains resolved to a small set of IP addresses — only 21 in total, with a single IP (199[.]59[.]243[.]160) resolving 32,716+ domains
🧬 Domain Patterns
The domain names follow repeating patterns such as:
traffic-accident-claim[.]shop
sciatica-treatment-24[.]live
accident-lawyer-help[.]online
pain-treatment[.]store
back-injury-settlement[.]site
These suggest the infrastructure is designed to target search engine ads (e.g., Google Ads) by mimicking legitimate services (law firms, medical aid, insurance, cars, vacation, rental, etc.).

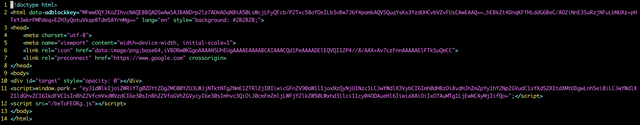
Here's always the same HTML retrieved:
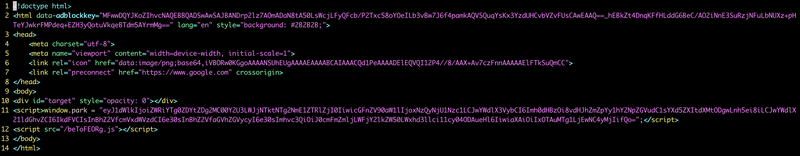
The script sets a global variable window.park containing a Base64-encoded JSON string. Decoding this typically reveals tracking details (such as a unique identifier, page time, URL, host, and IP address) used to tailor redirection or ad display.
The javascript core of this site
JavaScript Fingerprinting and Obfuscation
Each domain loads a JavaScript file via /beToFEORg.js — the same exact file across all 32k+ domains.
This consistency indicates:
Centralized infrastructure
Likely part of an ad parking or redirection system
Obfuscation and Encoding
A notable marker in the script:
const OBFUSCATING_BASE_64_PREFIX = "UxFdVMwNFNwN0wzODEybV";
this indicates heavy obfuscation.
This base64-like prefix is used across samples and can be treated as a detection fingerprint for similar scripts.
Additionally, after some deobfuscation , the script includes:
an Adblock class with removeAdblockKey():
removeAdblockKey() {
if (document.documentElement.dataset) {
delete document.documentElement.dataset.adblockkey;
}
}
Ad/Traffic Monetization Components
The script makes network requests to endpoints that look like part of an ad parking or traffic distribution system. For example:
TRACKING_DOMAIN is set to "https://click-use1[.]bodis[.]com/"
and
SALES_JS_URL is "https://parking[.]bodiscdn[.]com/js/inquiry.js".
It also includes functions such as getFindDomain and getZeroClick which perform POST requests (e.g. to /_fd and /_zc endpoints) that likely return configuration or tracking data.
This is used to evade or punish users with ad blockers.
Ad and Tracking Integrations
The script interacts with multiple ad networks and monetization platforms:
Primary endpoints:
https://click-use1[.]bodis[.]com/ (TRACKING_DOMAIN)
https://parking[.]bodiscdn[.]com/js/inquiry.js (SALES_JS_URL)
POST endpoints like /_fd and /_zc that likely return tracking config or redirect logic
Third-party integrations:
Facebook Pixel – https://connect[.]facebook[.]net/en_US/fbevents.js
Outbrain – //amplify.outbrain.com/cp/obtp.js
TikTok Analytics – https://analytics[.]tiktok[.]com/i18n/pixel/events.js
Taboola – cdn.taboola[.]com/libtrc/unip/${this.identifier}/tfa.js
This blend of adtech scripts and zero-click traffic handlers is typical in monetization networks, often used in:
Adware
Traffic monetization
SEO spam
Fake service landing pages
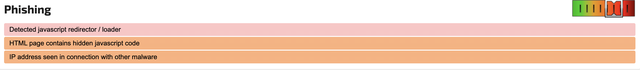
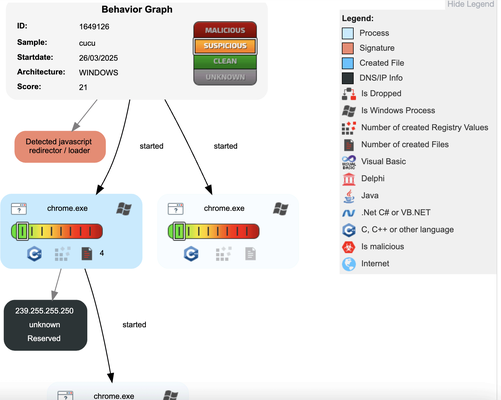
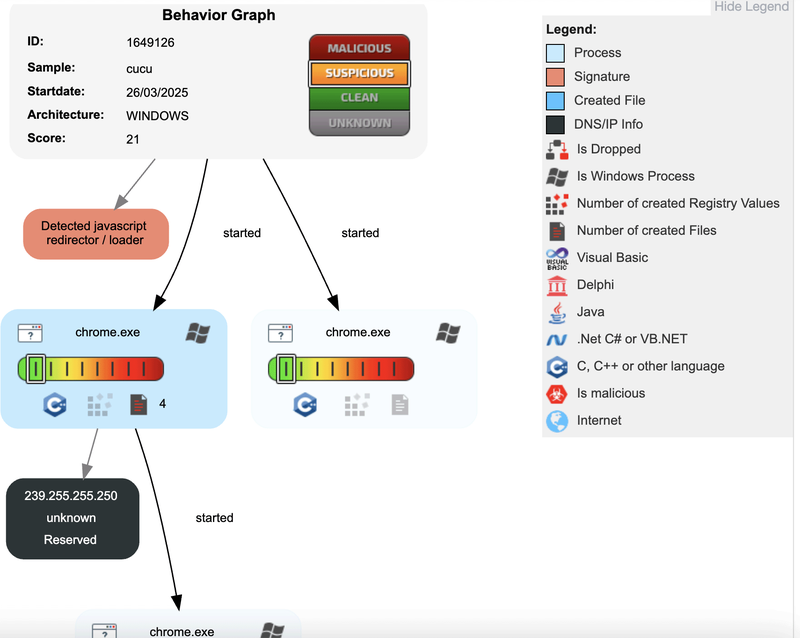
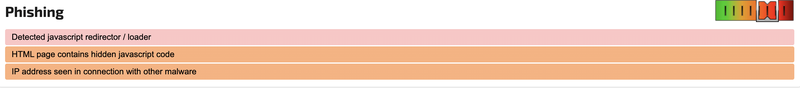
Sandbox results
As an example we queried a domain that resolves to 199[.]59[.]243[.]160
curl -k hxxps://007-accidentpain[.]shop > /tmp/cucu
Uploaded to JoeSandbox, the result categorized the file as:
Phishing
Associated with tracking and redirection behavior

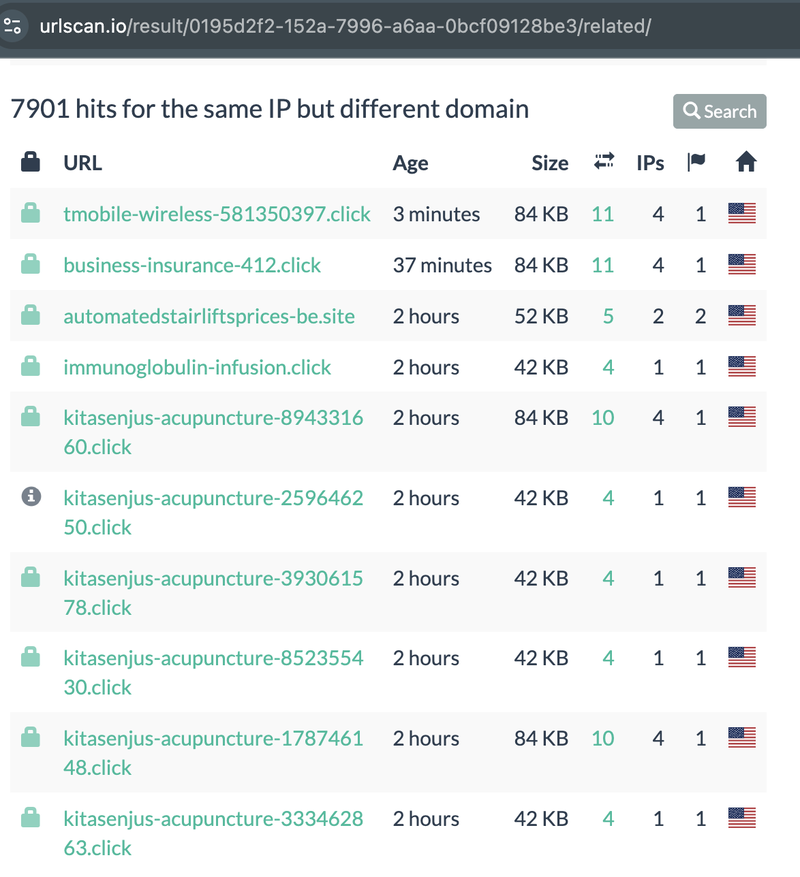
URLscan results
According to urlscan.io, there have been 7,900+ scans to domains resolving to the this same IP address (199[.]59[.]243[.]160). This reinforces the notion of a large-scale operation, with many domains actively observed and analyzed by researchers or automated systems.
IOCs
VirusTotal flags the IP address 199[.]59[.]243[.]160 with only two detections — one as Malware, another as Cryptominer.
https://www.virustotal.com/gui/url/9a908649043c924746df5215b5dc539e2f5fa5600047f1621763cc07702a7b74
Many associated domains trigger minimal alerts, with at most one engine categorizing them as Phishing or Suspicious.
These domains are often labeled by one or two AV engines on VirusTotal as:
Phishing
Suspicious
Miner
Malware
Or not flagged at all, indicating low AV coverage
199[.]59[.]243[.]160
Example domains
zerodownpaymentcarsae[.]site
zakelijke-credicard[.]cyou
weightlosstreatment0509[.]online
creditcardsforhorriblecredit[.]com
0-backpain-6[.]shop
bestmedicarequotes[.]net
Conclusion
While AV engines and sandboxes only partially detect this infrastructure, our DNS RPZ data and Domain Intelligence suggests a large-scale, coordinated adware network leveraging search traffic, domain churn, and tracking pixels.
We’re likely seeing just the tip of the iceberg.